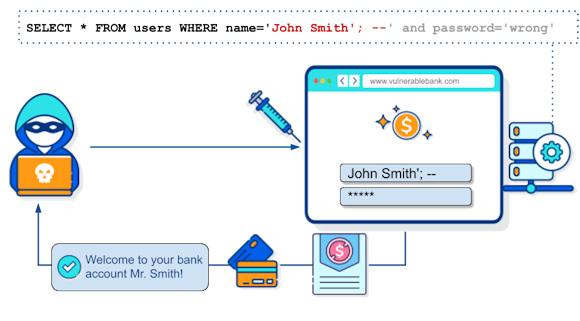
A few weeks ago I published an article entitled: "SQL Injection Attack: What is it?", sincerely thinking of saying things known to everyone and without therefore going too deeply into the matter...
In recent weeks I've had to change my mind!
In fact, many have contacted me asking for explanations and incredulous about the possibility of carrying out similar attacks.
Of course you will say: "But which planet do they come from???!". I'm not judging, also because I myself discover things every day, more or less banal for some, that I hadn't heard of.
The main questions focus on the real possibility of this attack: "Can you give me an example?", they ask me...
Here then is the need to write something more than what was already said in my previous article, not so much from a technical point of view but recalling some attacks.
Let's take for example the case made public by Information Week in 2009. A hacker group of probable Turkish origin, m0sted, attacked the website of an Army ammunition factory (McAlester Ammunition Plant in McAlester, Okla.) and the website of the US Army Corps of Engineers Transatlantic Center, in Winchester.
According to what was made public, the hackers used the technique of SQL Injection to exploit a vulnerability in Microsoft's SQL server database to access websites.
Once they gained access, the hackers modified some pages by inserting messages against the United States and Israel.
Let's look at another case. A few years later, in 2011, Sony Pictures suffered a similar attack. Approximately 77 million accounts on the PlayStation network were compromised for an estimated damage of approximately $170 million. The hackers managed to access the user database and personal data, including credit cards. In that case Sony blamed Anonymous of the theft of credit card data but publicly stated that he had no responsibility for the incident.
Naturally, since it is SQLi, the systems most at risk are those that use large databases. What's bigger than the databases of communication companies such as email providers?
In fact, in 2012 it is the turn of Yahoo! The hacker group known as D33D is the probable culprit of the attack against Yahoo's infrastructure, approximately 400.000 accounts were compromised in the attack.
I could continue with more recent examples but I think it is more useful to remind everyone that this type of attack continues to be one of the most used and it seems that programmers and database administrators do not learn much from history.
To support what I say you can take a look at the report Trustwave of June 2023. Based on a global network of "honeypots" (jars of honey, meaning false targets to attract hackers) the report analyzes the types of attacks against databases in some sensitive countries (Russia, Ukraine, Poland, UK, China and United States) trying to focus on the methods and techniques used. Interesting read for the more curious.
Thanks as always to the friends of Sicynt.
To learn more:
- https://www.itnews.com.au/news/hackers-hit-us-army-websites-146603
- https://www.informationweek.com/it-sectors/anti-u-s-hackers-infiltrate-a...
- https://www.theguardian.com/technology/2011/apr/26/playstation-network-h...
- https://www.theguardian.com/technology/blog/2011/may/05/anonymous-accuse...
- https://www.csmonitor.com/Technology/Horizons/2012/0712/Yahoo-hack-steal...
- https://siliconangle.com/2023/06/13/trustwave-report-finds-attacks-targe...
- https://www.trustwave.com/en-us/resources/blogs/spiderlabs-blog/honeypot...