However, not only commercial enterprises have been attacked by cybercriminals: health care companies, such as Community Healt Systems, financial ones, such as JPMorgan Chase & Co., and entertainment companies, such as Sony Pictures have also been victims of cyber attacks. All these acts have thus shaken the confidence in the security offered on the Internet.
The institutions were not inert: a particularly aggressive intervention saw the accusation by the US government of Chinese hackers of infiltrating American companies. There were also internationally coordinated interventions that led to the capture of high-profile cybercriminals, an example is the Onymous operation thanks to which numerous black market sites were discovered and interrupted including Silk Road which represented a flowing anonymous market. known for the illegal drug trade. The attack on the Net is not a passing fashion: if it is true that today information and personal data are the real wealth, we are witnessing a real raid of this "gold" in a world where more and more state and non-state actors state governments use the Internet and new technology to collect, process and store personal data that continue to be the subject of cyber-attacks for data supply.
The discussion about security and data breach in information technology is becoming more and more impregnating and growing among the media and the public. Some of these discussions may be counterproductive but increased awareness and debate on cyber threats is certainly good for security. More attention will therefore be paid to the dual use of technologies, such as for the Tor anonymous network, with the relative benefits for privacy but the problems in terms of security.
The exponential increase of the technological means suitable for the close connection between the individual and the Web will contribute to the growth of the phenomenon of hacking either by criminals or by consumers eager for an in-depth analysis of the products.
 Security remains a cost for companies but cybersecurity is not seen by everyone as a contingent problem, but a risk only for the larger ones. However, given the real danger that these attacks represent, the strengthening of cyber security represents a goal for 2015.
Security remains a cost for companies but cybersecurity is not seen by everyone as a contingent problem, but a risk only for the larger ones. However, given the real danger that these attacks represent, the strengthening of cyber security represents a goal for 2015.
Multi-factor authentication represents a good starting point in this panorama, in fact it would have probably been able to avoid the JPMorgan Chase & Co. violation. Even Apple Inc. learned the danger of cyber-violations too late: only after stealing a lot of celebrity data and photos - even in their intimate moments - decided to implement two-factor authentication for iCloud.
Institutions aimed at enforcing strict laws on disclosure of data profit from violations could also help. Today, however, there is no uniform framework in this area, think of the United States, home to the major data-violated companies, where each state has its own rules for cybersecurity. Certain data certainly need greater attention and are already protected by specific regulations such as those concerning health that see regard in the Health Insurance Portability and Accountability Act, regulations that must in any case be constantly updated to go hand in hand with progress. technological.
According to an analysis conducted by Verizon Communications Inc., third parties are only aware of 70/80% of the attacks, which suggests how the various states could strengthen monitoring capabilities and build risk awareness in users. Storing passwords in open files, for example, is a critical choice: if a hacker appropriated this file, he would have all the access keys in clear text. So you also have to pay close attention to filling out forms online. Cybersecurity must be placed not as a feature or as a convenience but as a real priority.
It is therefore very important to continue to invest in innovations in the field of computer security in view of the fact that the Web is comparable to a large safe in which all of us' data are stored, from the most known to the most sensitive. If any criminal, with good computer skills, were able to come into possession of valuable information, would he not be able to carry out any act he wants and of any entity representing a concrete threat to collective security?
Wouldn't it be possible to divert the missile by intervening on a remote missile control system?
Wouldn't it be possible to examine movements of people to plan terrorist actions?
Nicolò Giordana
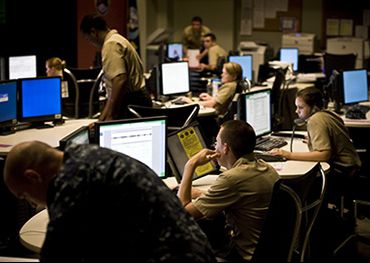
(photo: US Navy)












