Untangling the cybersecurity products, comparing them and then choosing them is not at all easy, even for experts. It is necessary to consider a multitude of different factors related to cyber threats and contextualize them within the specific business model of the company, to give priority to mitigation actions with the highest added value.
Anyone who offers web services, and we are talking about practically any organization offering online services, will have asked the question at least once: How to protect them?
Firewalls, in particular the so-called "latest generation" - Next generation firewalls, have the ability to inspect and filter traffic from the lowest (physical) to the highest (application) level of the ISO / OSI stack1. However, when it comes to web applications (the programs / software underlying all online services), they have somewhat limited functionality. For example, they may not be able to act as a "session terminator", meaning they can inspect HTTPS traffic, decrypt it temporarily, and then encrypt it back to the machine where the web application is actually running. Or they may not correctly handle particular encryption protocols (e.g. the most recent TLSv.32), HTTP protocols (e.g. version 2), or the analysis of the HTTP request / response fields and the body of such requests / responses. In these cases, web traffic analysis becomes very limited, if not impossible.
Put simply, the (next-generation) firewalls do not fully "understand" the information exchanged by web applications and therefore cannot adequately protect them from attacks, especially "one-shot" ones which also include one malicious request, and for which the lowest level filtering (e.g. based on the source IP address) is not sufficient.
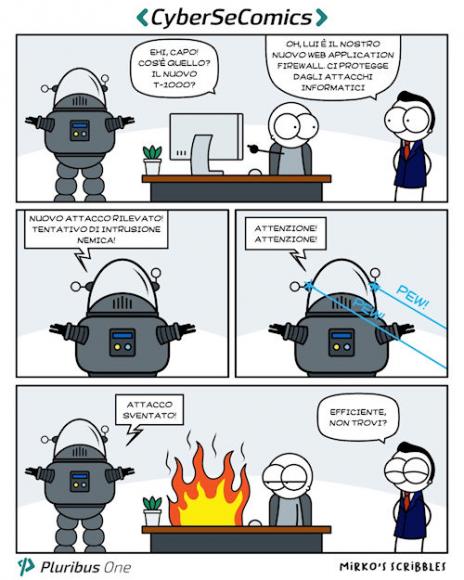
For this you need the Web Application Firewall (WAF), which provide functionality as complete as possible for understanding / managing HTTP (S) traffic, supporting the most recent protocols and information contents that can be associated with this level.
Problem solved? Unfortunately not.
Really understanding the functioning and the allowed and / or legitimate inputs / outputs of a web application is anything but trivial, even for developers, who increasingly know only some parts of the system. We could say that WAFs get where they can, through the typical use of known attack signatures (definitions) (typical illicit inputs) such as those provided free of charge by OWASP3 for the most popular open-source WAF, Modsecurity4.
But the devil is in the details. Such signatures are necessarily "generic" and require at least an important effort of "customization" in the production phase. Furthermore, they can only protect against certain instances of known attacks (on the basis of which these signatures have been produced), while web applications are ad-hoc programs, each different in its own way, and each with its user base that behaves in a certain way.
Basically, we need a system capable of analyzing events at a much greater level of abstraction than that offered by predefined signatures, a level in which the prerogatives of the monitored applications are evident and can therefore be detected. dangerous deviations for the underlying business to stop them before it's too late.