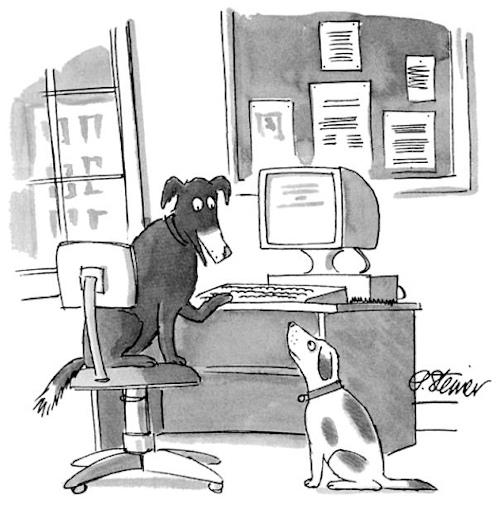
It's been 23 years since Peter Steiner published the infamous cartoon "On the Internet, nobody knows you're a dog" on The New Yorker, illustrating and, to some extent, anticipating in an eloquent and simple way the challenges related to online identity.
Today, many organizations are still struggling to solve the puzzle of whether those accessing information online are the proverbial "dog on the Internet", that is if "They are who they say they are and do not pretend to be someone else".
The consequences of this that has become a real war are significant: year after year the identity continues to be the most exploited vector of attack in cyberspace.
The biggest problem? Simple: the Password, continually violated and that, despite everything, continues to be used by everyone all over the world, whether we talk about companies or individuals and all seasoned with the chronic obstinacy or unconsciousness of no further protection which could be the use of multiple authentication factor solutions. This last phenomenon is extraordinary, alas, in companies.
The hacker world follows techniques and dynamics similar to industry, where supply and demand determine the price of a product. It is possible to buy the code of a exploit not yet known, the list of username e Password stolen from no matter where, individual credit card numbers guaranteed, still valid for at least a few days, etc. In short, a fantastic market where, by simply obscuring one's identity, one can make a bargain !!!
From all this derive phenomena such as the "Credential Stuffing" which is based on two of the weakest nodes of an entire security chain: the people and their Password.
The concept of "not using the same password on multiple sites" is very well known. We hear it repeated often and now, even more, even when we register on a new site. But how many people really use this foresight?

Obviously we are not talking about the experts, who use a manager of Password or similar mechanisms. We must think of the general public that is not so evolved from an IT point of view. In this context it is very likely that the same is used Password on well over two sites.
By exploiting this intrinsic vulnerability, an attacker specializes in finding combinations of username e Password valid. The first step is to buy in Dark web an archive of username e stolen passwords. With this database in your hands you start to try all the combinations on different sites in search of people who have used the same repeatedly login, often an email address, and the same Password. The end result is a distillate of username e Password valid on social media, email services, e-commerce whose value is very high as well as the fact that very often, the credentials used are the corporate ones. Here then is the use of the same Password on multiple sites it exposes personal information far beyond the "laundry" site.
The challenge with the Password, combined with other inadequate authentication methods, was amplified with the advent of cloud. The reason? Simple: the rise of the cloud combined with the explosion of mobile devices that make heavy use of them, it means that, increasingly, data is accessed outside of what was considered the network of an organization for which, unfortunately, checks are still being used. traditional security.
And here we return to the starting point, that is "In the cloud, the first question a system must answer is" are you who you say you are? " Let's never forget it: “authentication is the" key "to access the door of any cloud resource and, as I like to say, authentication is the heart of any infrastructure and represents the family jewels to defend at all costs and by any means.
Faced with a constantly growing phenomenon, biometric identification is considered by many to be the most immediate system for having access management that is, at the same time, reasonably secure and simple enough for those who must identify themselves.
 Apple's launch of the touch ID in the by now distant 2013, which offers users the possibility of unlocking their phones with their fingerprints or a PIN, has, in fact, defined the recognition of fingerprints as a new authentication factor, commercially distributed via smartphones .
Apple's launch of the touch ID in the by now distant 2013, which offers users the possibility of unlocking their phones with their fingerprints or a PIN, has, in fact, defined the recognition of fingerprints as a new authentication factor, commercially distributed via smartphones .
Today, fingerprint sensors are an offering on smartphones and laptops and facial recognition is also gaining ground. In addition to face and finger, today, iris, voice and heartbeat are three other biometric methods that are emerging on the market. Meanwhile, Apple has been joined by leading manufacturers including Microsoft, Lenovo, Samsung, LG and Fujitsu in the incorporation of biometric sensors into the devices.
From the authentication point of view, the implications of the phenomenon of "consumerisation" of biometrics are significant: rather than requiring a user to insert a Password or insert a token, biometrics allows a device to simply "recognize" a user. If properly configured, this system can lead to authentication experiences without Password which are much easier to use than other technologies.
In the cloud, where users expect immediate and on-demand access to applications and data, biometrics offers the possibility to simplify authentication, while improving the privacy and security. It is no coincidence that biometrics is helping the industry to overcome the limits of usability that have hampered the adoption of first generation authentication, favoring greater adoption of secure authentication tools throughout the market.
However, not all biometries are the same and some technologies and configurations can create significant risks for security and security privacy as well as regulatory and compliance challenges. These risks must be addressed in order to distribute the biometric factors in a responsible and safe manner.

At the heart of the problem is the fact that biometric technologies vary according to two fundamental principles:
⦁ The reliability of the devices regardless of the different authentication methods, ie face, fingerprints, iris, etc. The market is very diverse in this context and there are solutions that are highly reliable and others that are much less so. Two factors must always be taken into consideration:
- False Accept Rate (FAR) which indicates how often the biometric system accepts the biometrics of the wrong person;
- False Reject Rate (FRR) which indicates how often the biometric system rejects the biometrics of the right person.
⦁ The different ways in which biometric systems are designed and distributed can have a significant impact on the fact that they are able to improve safety and privacy or not.
An important difference between biometrics-based authentication modes and other authentication solutions is that the latter, like Password e token, can be modified or revoked. This means that if they are stolen or compromised, there is always a simple way to release a new solution and solve the problem.
Biometrics, on the other hand, is permanent and, therefore, the unintentional disclosure of biometric data can have more difficult consequences to correct than a simple Password violated. For this reason, any implementation of biometrics must be done with extreme care in order to mitigate the possibility that the fingerprint or someone's face, for example, may be compromised.
To mitigate IT risks, meet regulatory requirements and ensure access to resources in a simple and more secure way, authentication is increasingly required to protect users' identity against threats and, indirectly, protect their privacy .

The use of biometrics as an authentication mechanism, if implemented correctly and in compliance with the standards, can allow companies to protect their identity with a higher level than is still done today with the use of passwords.
There are still several questions and many doubts about the use of biometrics as an authentication methodology:
⦁ where are the biometric data stored?
⦁ where is the biometrics match made?
⦁ Is biometrics the only factor required to authenticate?
⦁ How are biometric information protected?
We leave the answers unanswered for the moment, with the promise to investigate them soon.
Photo: web / US Air Force / US Air National Guard