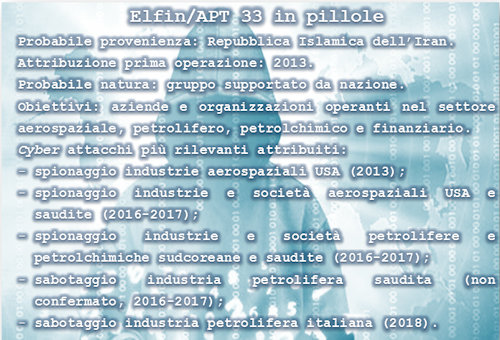
Elfin, "Elfo" in Italian, is the code name that the computer security company Symantec has attributed to a group of hackers who, presumably, is linked in some way to the Islamic Republic of Iran. This nickname, decidedly more captivating than the anonymous acronym APT 33, with which the organization in question is universally known, should not be misleading. On the contrary, the wave of cyber attacks that involved the Italian company SAIPEM last December (Italian company that offers services to companies operating in the oil sector - v. article) shows that the Elf is able to hit even harder than it did in the past.
APT 33 has a history that, although relatively recent compared with the events of other cyber groups, is very respectable as regards both the proven attack capabilities and the value of the targets hit. In particular, researchers in cybersecurity issues follow Elfin's operations from the 2013, but do not exclude that the group has taken its first steps in cyberspace since a few years earlier. Analysts believe that APT 33 is involved in several campaigns conducted primarily against targets located in the US, Saudi Arabia, the United Arab Emirates, Qatar and South Korea. Specifically, they are mostly companies and organizations operating in the aerospace sector. both military and civil, in the energy sector, with particular reference to the oil and petrochemical companies, and the financial one.
It should be pointed out that APT 33 has operated in two different ways according to the nationality of the objectives. In fact, if compared to the USA and South Korea, the group has mainly conducted cyber-espionage campaigns, against companies and organizations based in the Middle East has instead launched real "destructive" attacks (blocking of business activities, destruction of data, damage to systems, etc.). It is therefore a group with significant and varied cyber-offensive skills and for this reason the experts believe that it is probably supported by a nation. Moreover, the cyber capabilities of the Elfo have become increasingly refined over time, demonstrating that it has at its disposal considerable personnel resources, continuously trained and updated, and financial resources, necessary for the development of increasingly sophisticated attack vectors.
In particular, the most used technique by APT 33 to gain access to systems and networks of objectives is that of spear phishing, ie through the sending of artificial and misleading e-mails to persons who hold special positions within the target organization (managers, IT systems administrators, specialized technicians, etc.). These fraudulent communications are conceived by the Elf in a particularly refined manner, so that, in most cases, they are considered by the unfortunate as original and of particular interest for the performance of their respective duties. In reality, they induce the user to perform certain apparently legitimate operations, which instead allow the introduction into the target systems of the software specially prepared by Elfin, the so-called malware, bypassing the organization's information security systems.
It has been shown that the group is able to conduct its attacks by developing different modules of malware interacting with each other, they allow APT 33 to perform illicit actions, which can range from data theft, to their destruction without the possibility of recovery, to the complete blockage of the affected systems. Specifically, in the latest wave of cyber attacks involving SAIPEM, a variant of the malware known as SHAMOON, already used in previous attacks. This time, in addition to damaging the memories of PCs and servers containing operating systems, essential for their operation, has also deleted all other data stored, without the possibility of being able to recover with the techniques currently known. Briefly, the malware is not limited to "formatting" the disks, but it also overwrites the content several times, following precise algorithms so that it is impossible to recover them (in this case the malware it is defined wiper). Ultimately, SHAMOON can determine not only the momentary blockage of the activities of the target hit, but also can make the actions of data recovery and recovery of normal operations very difficult.
Unlike similar previous attacks, from the first analysis of the variant of the wiper more recently used, it emerged that the operation was carried out through an "active" role of the human component, that is through the execution of instructions given manually. This suggests that the "destructive" phase of the attack was preceded by a massive theft of confidential data that had to be preserved from possible accidental damage. In this regard, it should be pointed out that during this period SAIPEM is engaged in some negotiations for the awarding of major contracts in the Persian Gulf area by the oil company Saudi ARAMCO (which has already been heavily hit by similar cyber attacks in the past). So this is about industrial espionage or sabotage? Or of both? And the goals are related to mere commercial competition or are they aimed at the failure of the negotiations to the detriment of a specific part? These are questions that no one, for now, can give an answer that goes beyond the hypothesis. To complicate the investigation, finally, there is the fact that the attack would have originated in India. However, it may just be an attempted deception by the group of hackers, a tactic adopted very frequently in the landscape of well-planned and sophisticated cyber attacks.
In this ambiguous context, analysts believe that APT 33 is somehow linked to Iran. Excluding the appropriate general considerations on the ability to attribute the paternity of cyber attacks and on the ability to determine their originators, analysts believe that there is substantial evidence of precise links between Elfin and the Nasr Institute, controlled by the Iranian government and connected, in turn, with the Iranian Cyber Army (another group of hackers). On the other hand, the aims of the cyber campaigns of APT 33 perfectly fit with certain aspects of Iranian foreign policy and also the timing with which some "destructive" attacks were perpetrated coincide with certain moments of political tension between the Islamic Republic and countries involved. Many other clues collected by examining i malware employed by the group would support the thesis that this organization would operate on behalf of Iran. For example, by examining the new variant of the wiper a fragment of programming code has been isolated which, displayed on the screen, materializes a passage from the Koran in Arabic (see picture).
 More precisely, according to some, APT33 would be framed within the ambitious program of development of cyber capabilities both defensive and offensive, which was launched by Iran in the aftermath of the known cybernetic attack suffered at the Natanz nuclear power plant in the 2010 (v. article). It was probably in that circumstance that Iran understood the real potentialities offered by the cyber war and, above all, its dramatic effects in the "real" world. It was a particularly painful lesson but evidently also constituted a turning point. Since then, in a relatively few years, Iran has implemented sophisticated cyber capabilities that were initially greatly underestimated and, in some cases, also seen with a certain sufficiency.
More precisely, according to some, APT33 would be framed within the ambitious program of development of cyber capabilities both defensive and offensive, which was launched by Iran in the aftermath of the known cybernetic attack suffered at the Natanz nuclear power plant in the 2010 (v. article). It was probably in that circumstance that Iran understood the real potentialities offered by the cyber war and, above all, its dramatic effects in the "real" world. It was a particularly painful lesson but evidently also constituted a turning point. Since then, in a relatively few years, Iran has implemented sophisticated cyber capabilities that were initially greatly underestimated and, in some cases, also seen with a certain sufficiency.
It is worth recalling once again the extreme opacity of cyberspace, a dimension in which individual hackers, intelligence services, armed forces, political activist groups, even terrorist or subversive groups, as well as criminal organizations that, thanks to cyber crime, bill millions of dollars every year. Moreover, in many cases some of these subjects cooperate with each other more or less consciously, thus contributing to making cyber reality extremely ambiguous and dangerous. One thing is certain, whether or not it is linked to Iran, whether it be a group of mercenary hackers or state or military officials, rather than political activists, APT 33, through the attack last December, has not only achieved its tactical objectives related to the specific need, but also launched a precise warning to the whole world: the Elf is bad, and is able to "hit hard" critical private and public infrastructures, those that should be defended more effectively. In short, Elfin has definitely been credited among the most dangerous groups of hackers in the world, absolutely not to be underestimated!
Finally, some questions. This time it would seem that the wiper has operated following instructions given manually, but what if, in the future, he acted in full autonomy and escaped control of the attacker? The proliferation of cyber weapons, of which someone is stubborn to not recognize the danger (perhaps because it is not able to understand the value that the data have assumed in today's era) is a matter repeatedly highlighted by Difesaonline, but which is not yet adequately addressed by the appropriate institutions. Furthermore, if indeed APT 33 is linked to Iran, why are not among its targets for striking attacks such as the most recent Israeli ones, given the ongoing tensions between their respective governments? This is perhaps a matter of deterrence, considering that the Israelis are probably the most avant-garde in this field (v. article)? Is it for the same reason that Elfin does not "hit hard" the US objectives? If this were the case, it would be the demonstration that, even in cyber space, the best strategy to defend oneself is to demonstrate that one is able to fight back.
Probably, after the political hypocrisy of the facade, it would be appropriate to admit that, in the context of an effective cyber security strategy, cyber deterrence should have a weight at least equal to that of the Cyber Defense measures.
Main sources:
https://www.fireeye.com/blog/threat-research/2017/09/apt33-insights-into...
https://attack.mitre.org/groups/G0064/
https://www.ts-way.com/it/weekly-threats/2018/12/28/weekly-threats-n-42-...
https://www.symantec.com/blogs/threat-intelligence/shamoon-destructive-t...
https://www.zdnet.com/article/shamoons-data-wiping-malware-believed-to-b...
https://securingtomorrow.mcafee.com/other-blogs/mcafee-labs/shamoon-atta...
https://www.reuters.com/article/iran-cyber/once-kittens-in-cyber-spy-wor...
https://www.cybersecurity360.it/nuove-minacce/saipem-attacco-di-cyber-sa...
www.google.it/amp/s/www.wired.com/story/iran-hacks-nuclear-deal-shamoon -...
www.milanofinanza.it/amp/news/saipem-possibile-commessa-offshore-da-saud ...












